Slide 1 - Containment and Eradication
Containment and Eradication: Protecting Systems and Populations
A Comprehensive Framework for Incident Response and Disease Control
---
Photo by Adi Goldstein on Unsplash

Generated from prompt:
Make a presentation about
This deck presents a comprehensive framework for containment and eradication in cybersecurity incident response and disease control, drawing parallels between medical triage and cyber defense. It covers incident logic, dual containment strategies, Er
Containment and Eradication: Protecting Systems and Populations
A Comprehensive Framework for Incident Response and Disease Control
---
Photo by Adi Goldstein on Unsplash

---
Photo by Logan Voss on Unsplash
1
Drawing parallels between medical triage and cybersecurity defense
---
Photo by National Institute of Allergy and Infectious Diseases on Unsplash

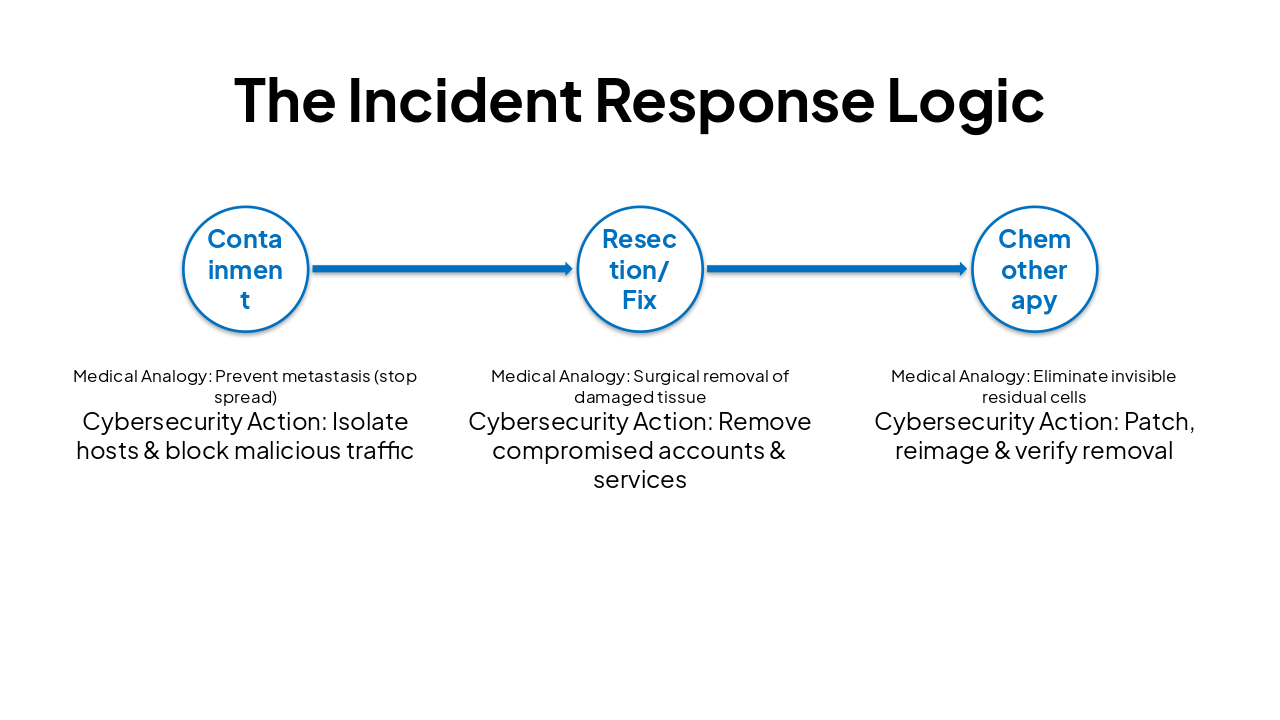
| Phase | Medical Analogy | Cybersecurity Action |
|---|---|---|
| Containment | Prevent metastasis (stop spread) | Isolate hosts & block malicious traffic |
| Resection/Fix | Surgical removal of damaged tissue | Remove compromised accounts & services |
| Chemotherapy | Eliminate invisible residual cells | Patch, reimage & verify removal |
2
Immediate actions to stop the bleeding and maintain operations
---
Photo by Fabian Kleiser on Unsplash
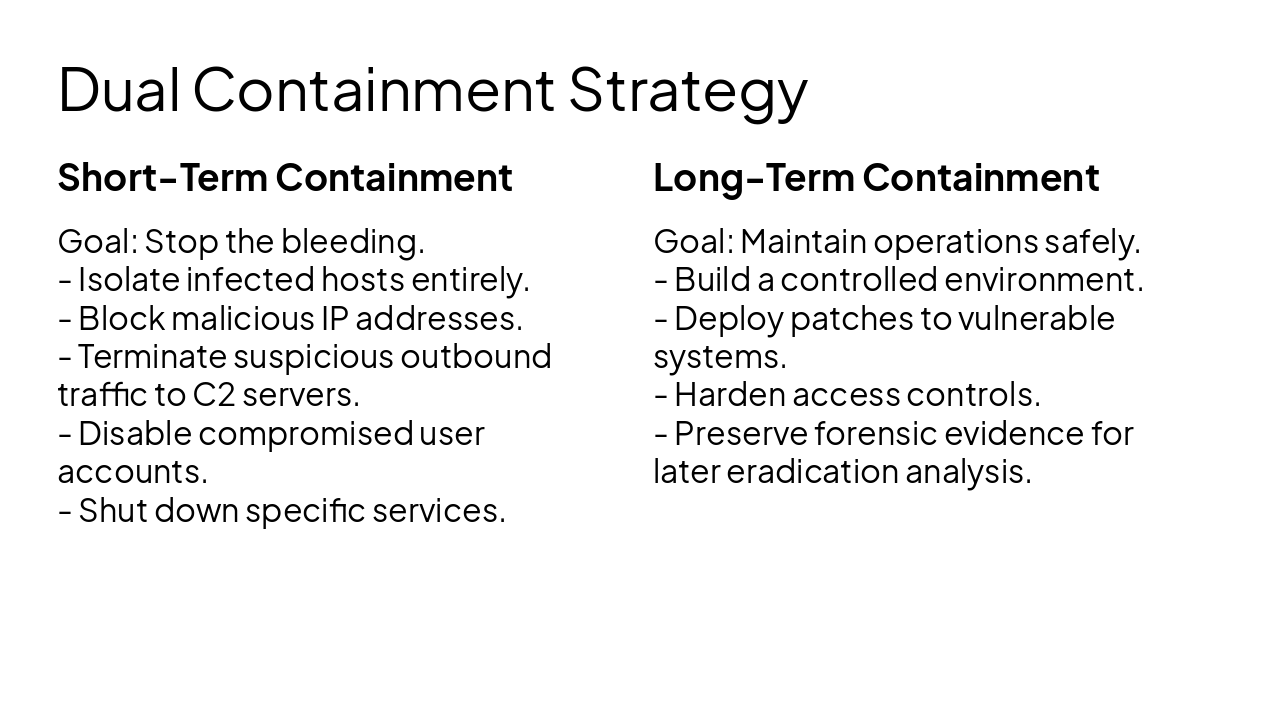
Short-Term Containment Goal: Stop the bleeding.
Long-Term Containment Goal: Maintain operations safely.
3
Removing every trace and confirming a clean slate
4
Learning from past failures and success stories
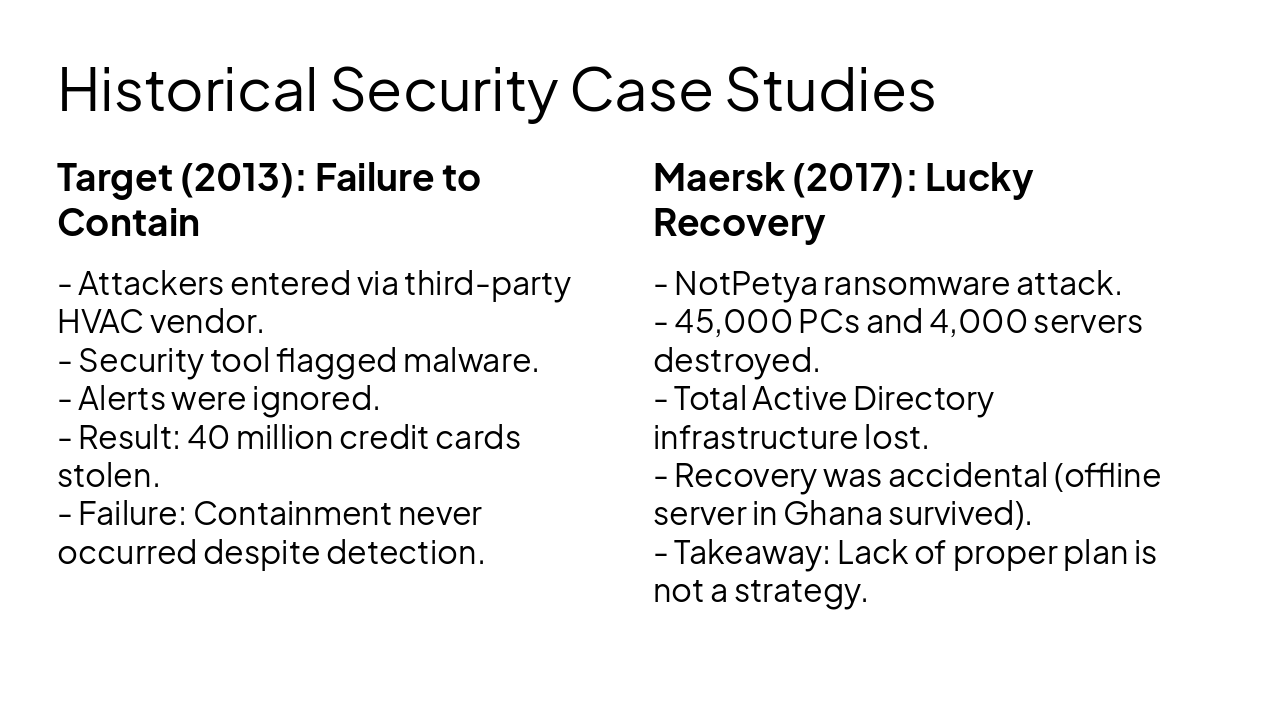
Target (2013): Failure to Contain
Maersk (2017): Lucky Recovery
Plan, Contain, Eradicate, Verify.
Containment is about buying time; Eradication is about restoring integrity. Always confirm clean.
---
Photo by jack atkinson on Unsplash
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.