Slide 1 - Meltdown and Spectre
Critical CPU Vulnerabilities Affecting Intel Processors
Speculative Execution Side-Channel Attacks

Generated from prompt:
make a detailed presentation about meltdown and specter vulnerabilities on intel cpus
This presentation provides an in-depth overview of the Meltdown (CVE-2017-5754) and Spectre (CVE-2017-5753/5715) vulnerabilities, explaining speculative execution as the root cause, attack mechanisms, performance impacts, key differences, historical
Critical CPU Vulnerabilities Affecting Intel Processors
Speculative Execution Side-Channel Attacks

---
Photo by Aleksandrs Karevs on Unsplash

1
Root cause of Meltdown and Spectre
---
Photo by razi pouri on Unsplash
Source: Wikipedia: Transient execution CPU vulnerability
---
Photo by Devin Spell on Unsplash
Source: Wikipedia: Spectre
> Meltdown affects Intel x86 microprocessors, IBM Power microprocessors, and some ARM-based microprocessors. It allows a rogue process to read all memory, even when it is not authorized to do so.
— Wikipedia: Meltdown (security vulnerability)
Source: Wikipedia: Meltdown
Source: Wikipedia: Meltdown
Source: Wikipedia: Meltdown

3
CVE-2017-5753 (V1) & CVE-2017-5715 (V2)
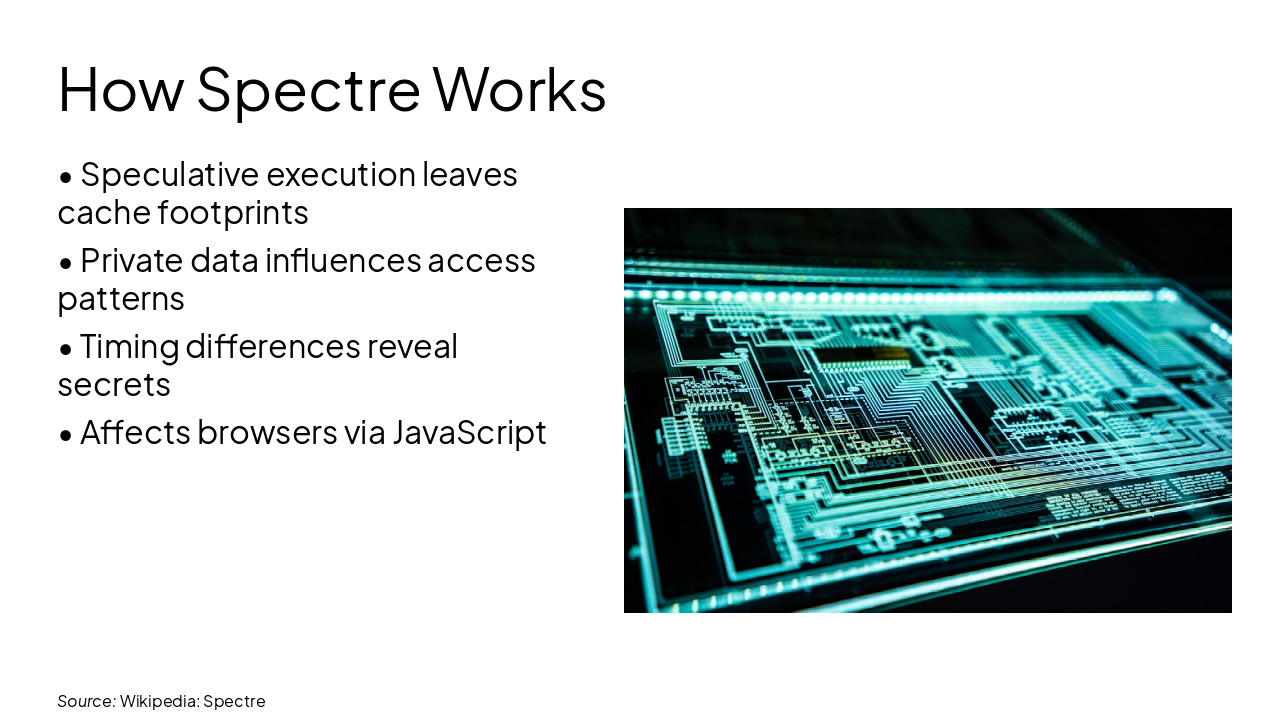
Spectre V1 (CVE-2017-5753) Bounds check bypass using speculative execution to ignore array bounds, leaking cross-process data via cache timing.
Spectre V2 (CVE-2017-5715) Branch target injection manipulates indirect branches, forcing speculation to malicious code paths for data extraction.
Source: Wikipedia: Spectre
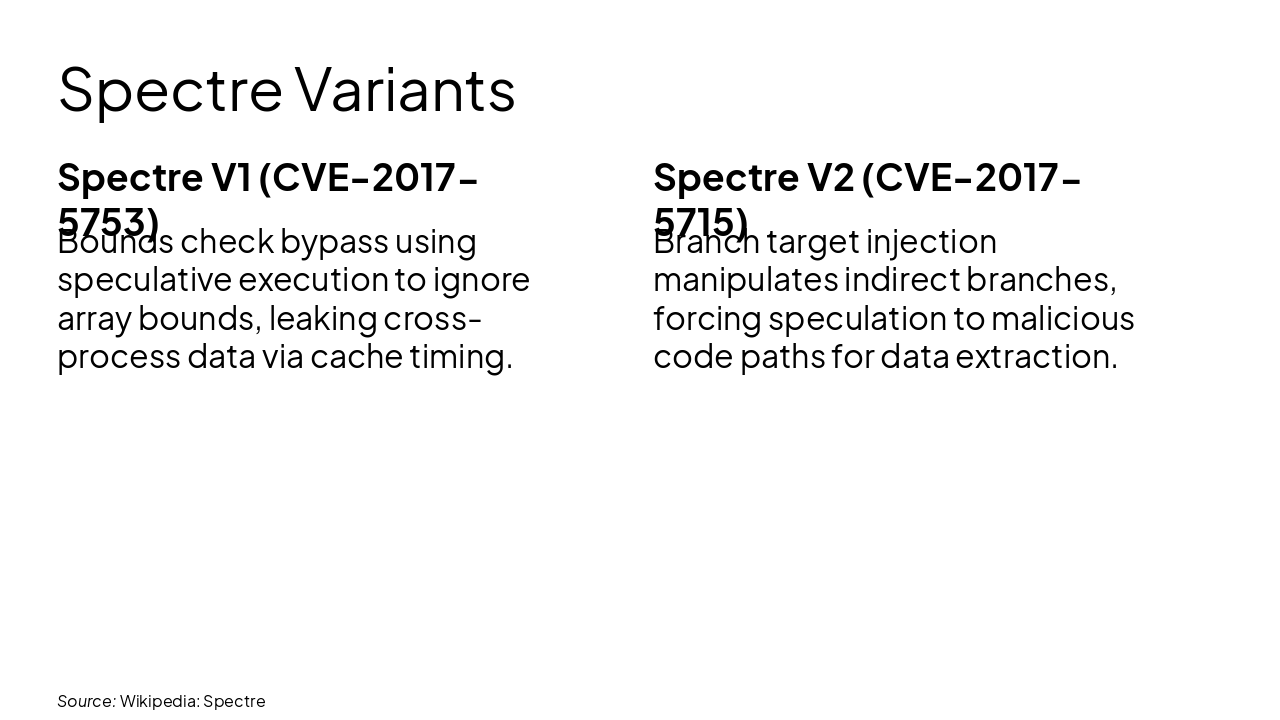
Source: Wikipedia: Spectre
---
Photo by Adi Goldstein on Unsplash
Source: Wikipedia: Spectre
4
Severity and Performance Trade-offs

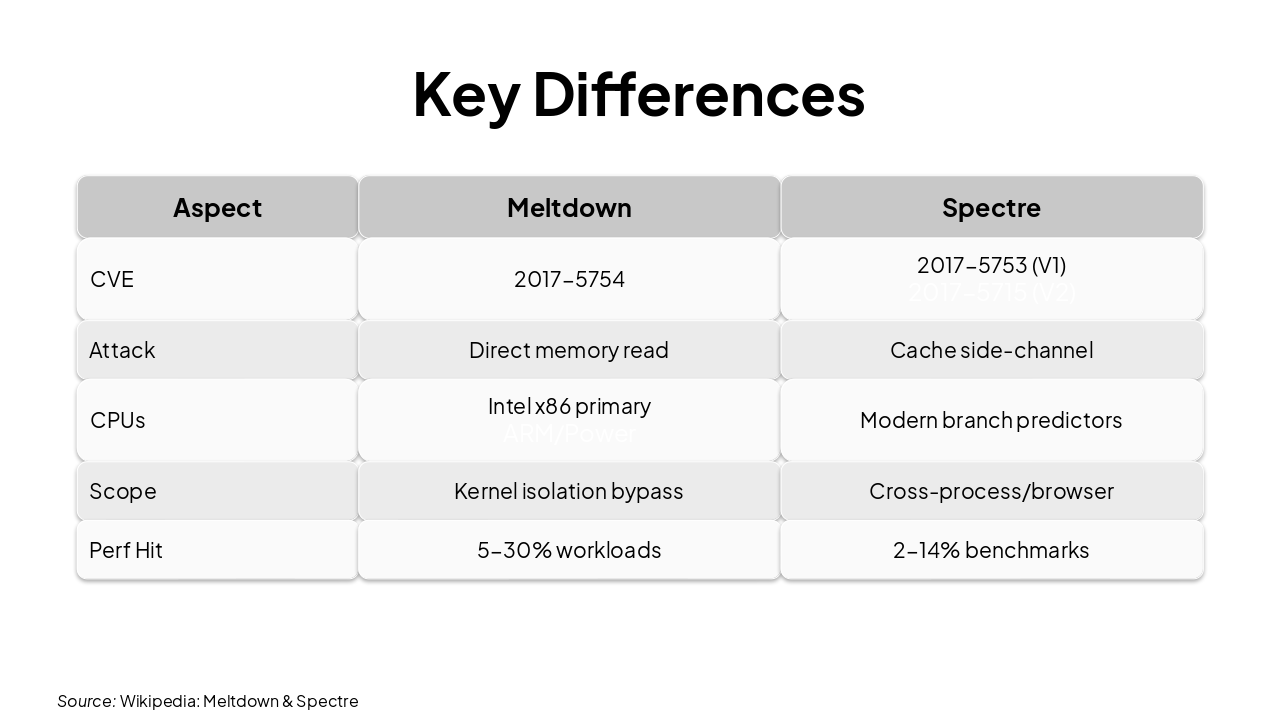
| Aspect | Meltdown | Spectre |
|---|
| CVE | 2017-5754 | 2017-5753 (V1) 2017-5715 (V2) |
| Attack | Direct memory read | Cache side-channel |
|---|
| CPUs | Intel x86 primary ARM/Power | Modern branch predictors |
| Scope | Kernel isolation bypass | Cross-process/browser |
|---|---|---|
| Perf Hit | 5-30% workloads | 2-14% benchmarks |
Source: Wikipedia: Meltdown & Spectre
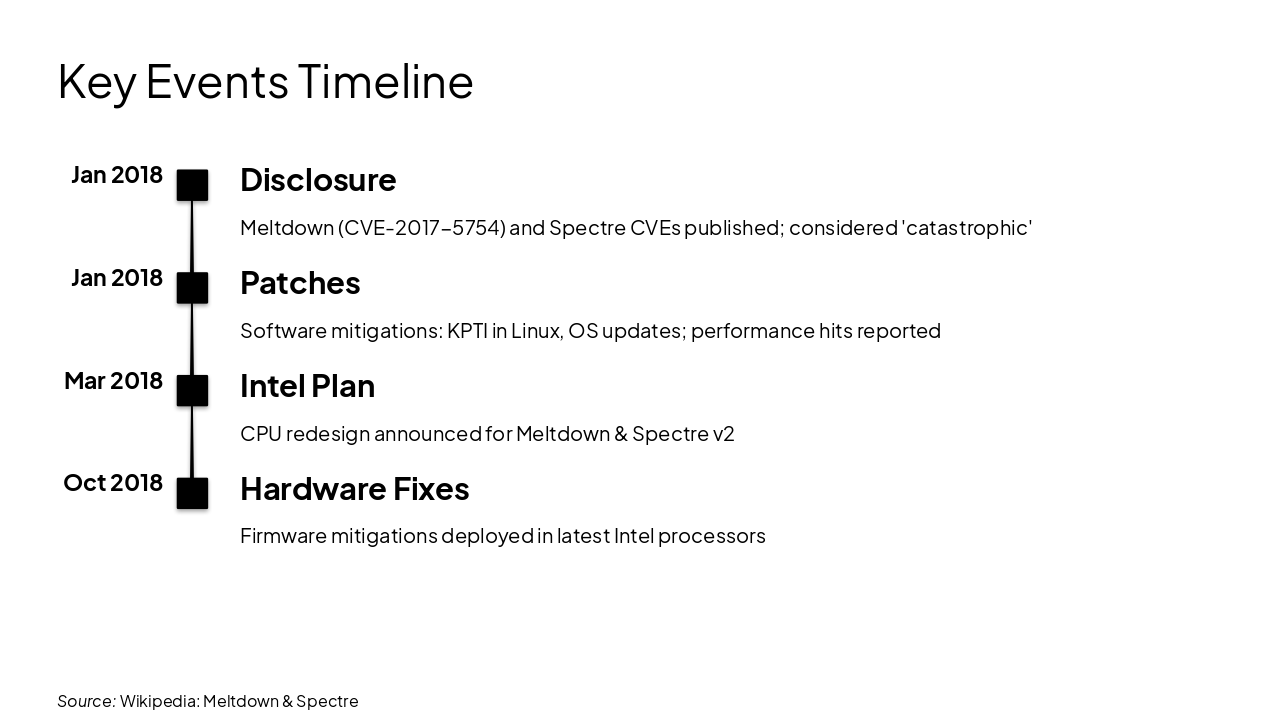
Jan 2018: Disclosure Meltdown (CVE-2017-5754) and Spectre CVEs published; considered 'catastrophic' Jan 2018: Patches Software mitigations: KPTI in Linux, OS updates; performance hits reported Mar 2018: Intel Plan CPU redesign announced for Meltdown & Spectre v2 Oct 2018: Hardware Fixes Firmware mitigations deployed in latest Intel processors
Source: Wikipedia: Meltdown & Spectre
5
From KPTI to Hardware Redesign
---
Photo by Jakub Żerdzicki on Unsplash
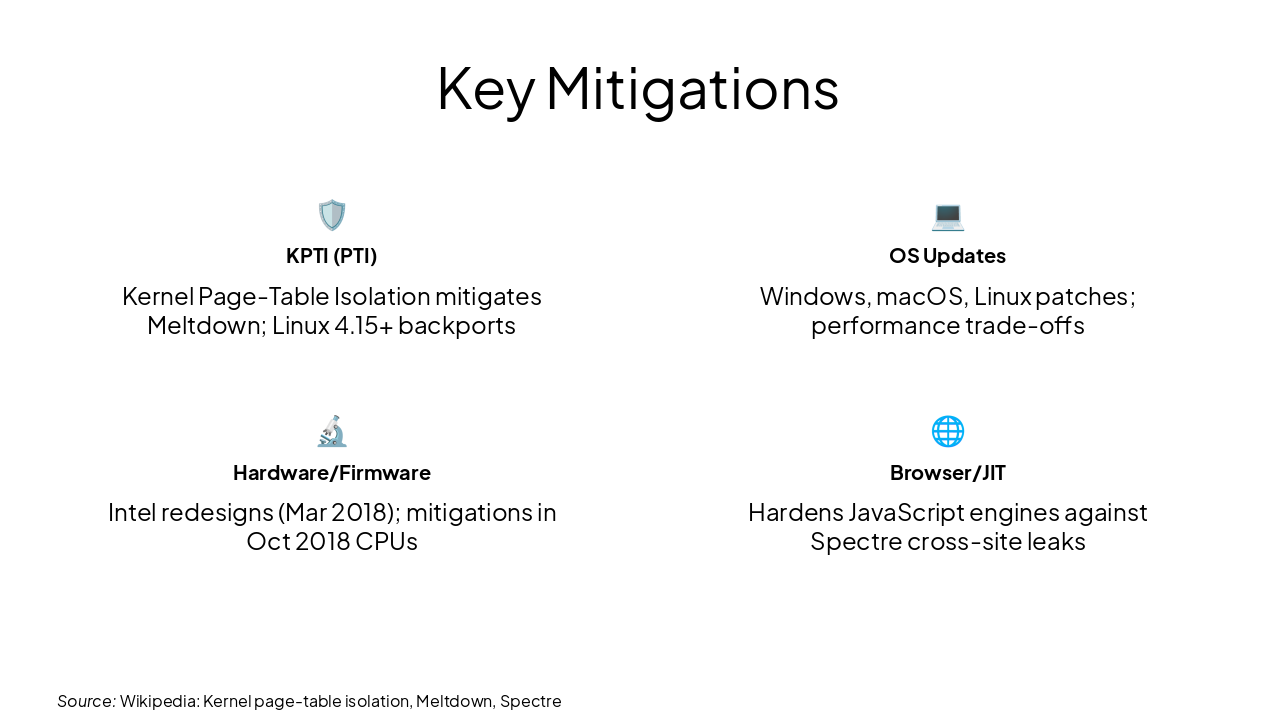
🛡️ KPTI (PTI) Kernel Page-Table Isolation mitigates Meltdown; Linux 4.15+ backports
💻 OS Updates Windows, macOS, Linux patches; performance trade-offs
🔬 Hardware/Firmware Intel redesigns (Mar 2018); mitigations in Oct 2018 CPUs
🌐 Browser/JIT Hardens JavaScript engines against Spectre cross-site leaks
Source: Wikipedia: Kernel page-table isolation, Meltdown, Spectre
Meltdown & Spectre: Catastrophic but mitigable
Apply patches promptly Monitor hardware updates Balance security & performance
Questions? Thank you!
---
Photo by Hyunwon Jang on Unsplash

Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.