Slide 1 - ISO/IEC 27001:2022 Awareness Training
ISO/IEC 27001:2022 Information Security Awareness Training
Building a Secure Workplace Together
---
Photo by Tom Parkes on Unsplash

Generated from prompt:
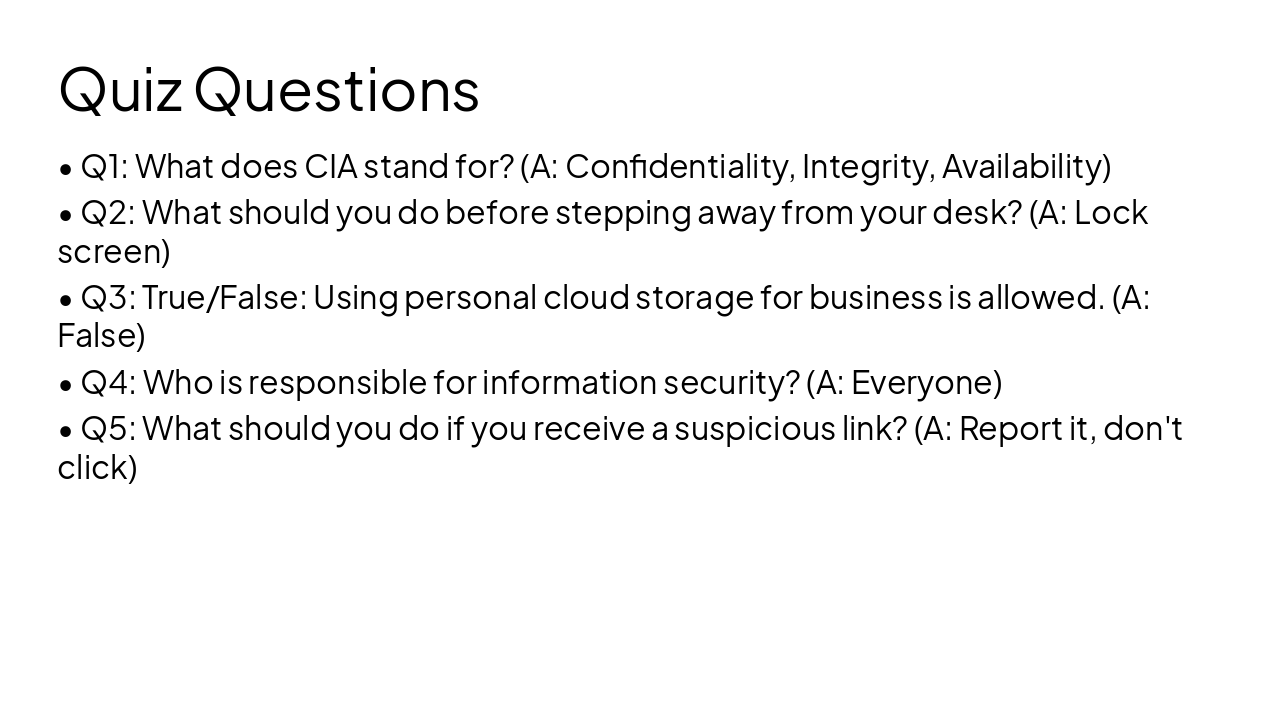
Create a 1-hour training PowerPoint: ISO/IEC 27001:2022 Information Security Awareness for Employees. Audience: all employees in a company preparing for ISO 27001 certification. Approx 35–40 slides suitable for a 60-minute session. Include speaker-friendly bullets and simple examples. Structure: 1) Title & objectives, 2) What is information security and why it matters (with real-world breach examples), 3) Overview of ISO/IEC 27001:2022 and certification journey, 4) CIA triad (confidentiality, integrity, availability), 5) What an ISMS is and how employees support it, 6) Roles & responsibilities of employees, 7) Information classification & handling, 8) Acceptable use of company assets, 9) Passwords, MFA, and authentication hygiene, 10) Phishing & social engineering awareness with examples, 11) Email and internet security, 12) Safe use of cloud tools and file sharing, 13) Remote work and mobile device security, 14) Clean desk & clear screen practices, 15) Physical security basics, 16) Data protection & privacy considerations, 17) Incident identification and reporting process, 18) Overview of Annex A controls (high-level employee-relevant controls), 19) Consequences of non-compliance and real risk scenarios, 20) What to do if something goes wrong, 21) Quick recap of employee do’s and don’ts, 22) Short knowledge check quiz (5–7 questions), 23) Closing slide with key takeaways. Make slides visually clear and appropriate for corporate training.
This deck delivers essential ISO/IEC 27001:2022 awareness training for employees, covering information security fundamentals, CIA triad, ISMS overview, roles and responsibilities, authentication hygiene, phishing defense, data handling, physical and遥
ISO/IEC 27001:2022 Information Security Awareness Training
Building a Secure Workplace Together
---
Photo by Tom Parkes on Unsplash

---
Photo by Sebastian Svenson on Unsplash
2
Certification Journey & Our System
---
Photo by Conny Schneider on Unsplash

3
How You Support Our Security
---
Photo by Israel Andrade on Unsplash

4
Passwords, MFA, and Phishing
---
Photo by Adi Goldstein on Unsplash

5
Physical, Digital, and Remote Security
---
Photo by Pieter de Boer on Unsplash
6
Incident Response & Reporting
---
Photo by Jay Openiano on Unsplash
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.