Slide 1 - Social Engineering and Phishing
Social Engineering and Phishing
Cybersecurity Threats and Prevention
---
Photo by Luis Quintero on Unsplash

Generated from prompt:
It's on the topic of social engineering and phishing
This presentation provides an in-depth look at social engineering and phishing, key cybersecurity threats. It covers definitions, psychological manipulation tactics, various phishing types including email, vishing, smishing, spear phishing, and emerging trends like quishing and deepfakes. Backed by statistics showing phishing as the top cybercrime affecting most businesses, it includes real examples and concludes with essential prevention strategies such as user education, technical filters, multi-factor authentication, and verification practices.
Social Engineering and Phishing
Cybersecurity Threats and Prevention
---
Photo by Luis Quintero on Unsplash

---
Photo by Logan Voss on Unsplash

1
Manipulating Human Psychology for Information Access
---
Photo by Musemind UX Agency on Unsplash

Source: Wikipedia: Social engineering (security)

Source: Wikipedia: Phishing
---
Photo by Logan Voss on Unsplash
Source: Wikipedia: Phishing
Source: Wikipedia: Phishing
---
Photo by Matthew Fournier on Unsplash
Source: Wikipedia: Phishing
3
Using Telephony to Steal Information
---
Photo by Kaptured by Kasia on Unsplash
Source: Wikipedia: Voice phishing
Source: Wikipedia: Phishing
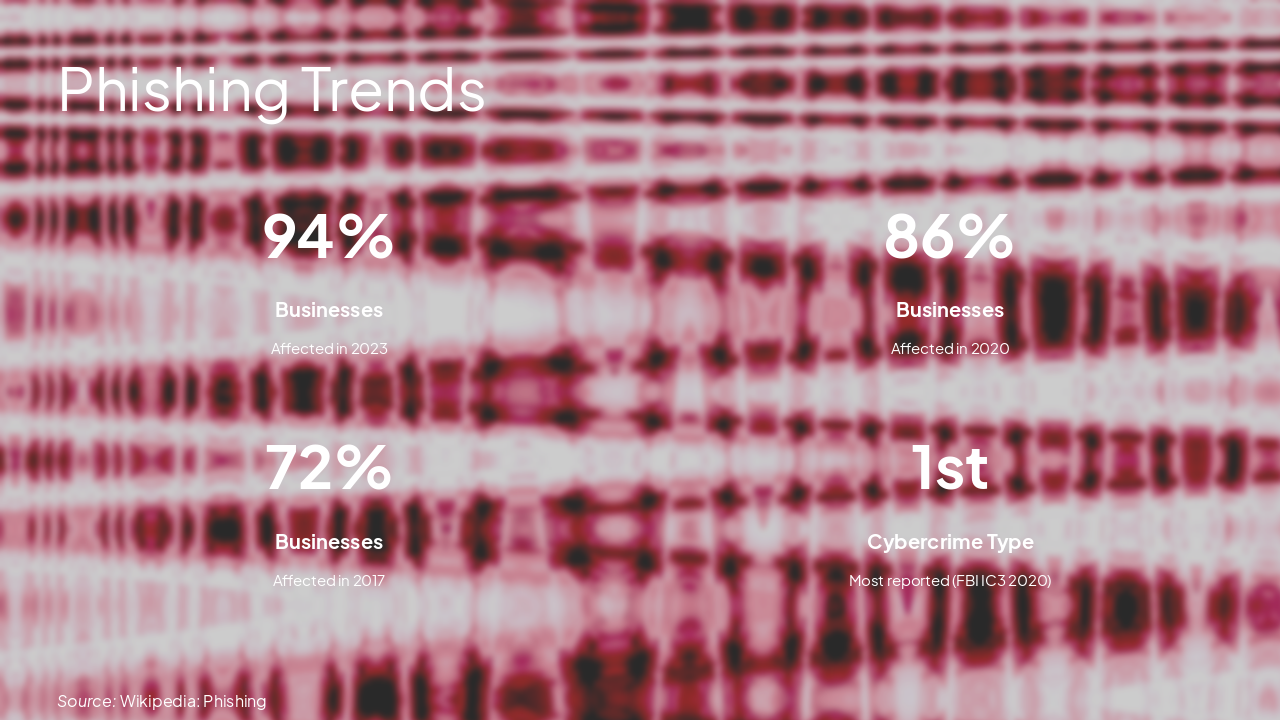
> As of 2020, it is the most common type of cybercrime, with the FBI's IC3 reporting more phishing incidents than any other cybercrime.
— Wikipedia: Phishing
---
Photo by Danish Prakash on Unsplash
Source: Wikipedia: Phishing
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.