Slide 1 - Digital Forensic Case Briefing: Narcos Investigation
Digital Forensic Case Briefing: Narcos Investigation
KV5041 Digital Forensics Incident Response | Senior Investigator Briefing
---
Photo by Giannis Skarlatos on Unsplash

Generated from prompt:
Create a master's-level forensic investigation presentation (10 minutes, ~8 slides) titled 'Digital Forensic Case Briefing – Narcos Investigation'. Audience: senior investigators. The presentation synthesizes evidence from three suspects (John Fredricksen, Jane Esteban, Steve Kowhai) but emphasizes the Jane Esteban forensic findings provided in the report. Slides should be visually professional with headings, concise bullets, and placeholders to insert screenshots from the report exhibits. Slides structure: 1. Title Slide – Digital Forensic Case Briefing: Narcos Investigation (KV5041 Digital Forensics Incident Response). 2. Case Overview – seizure of methamphetamine at NZ Customs, suspects John Fredricksen, Jane Esteban, Steve Kowhai, objective of digital forensic investigation. 3. Investigation Methodology – tools used (Autopsy, FTK Imager, Volatility 3, Kali Linux, hash verification) and evidence sources (disk image, memory dump, artefact recovery). 4. Jane Esteban – Web History & Behavioural Evidence – searches about smuggling, customs evasion, undercover survival; use of ProtonMail and Discord; Quasar RAT download (insert screenshot placeholders from report exhibits). 5. Digital Artefacts & Deleted Evidence – recovered files (bag_contents.jpg showing suitcase concealment, contact_list.txt, travel_plans.docx), meth images (crys1–3), deleted AFP logo; significance for intent and knowledge. 6. Device Interaction & Coordination – USB device history, shellbags showing external drives and folder 'John', contact card files; suggests collaboration and data exchange. 7. Memory Forensics – Quasar RAT running, command-and-control connection to 202.2.12.15:4782, suspicious ManagementAgent spawning cmd.exe, implications for remote coordination. 8. Synthesised Case Analysis – unified timeline, links between suspects, corroboration across disk, memory and deleted artefacts; evidence of conspiracy and coordination. 9. Overall Evidential Strength & Conclusion – strong digital evidence, contradiction of innocent courier defence, recommendations for further investigation (email warrants, C2 IP analysis, cross-device correlation). Design guidance: dark professional forensic theme, icons for evidence types, space for screenshots, diagrams for timeline and network connection. Ensure content suitable for a 10‑minute group presentation where three members each present sections.
Comprehensive briefing on digital forensic analysis of devices seized in a methamphetamine smuggling case at NZ Customs. Covers investigation methodology, web history, recovered artefacts, device coordination, memory forensics, and synthesized case結論
Digital Forensic Case Briefing: Narcos Investigation
KV5041 Digital Forensics Incident Response | Senior Investigator Briefing
---
Photo by Giannis Skarlatos on Unsplash

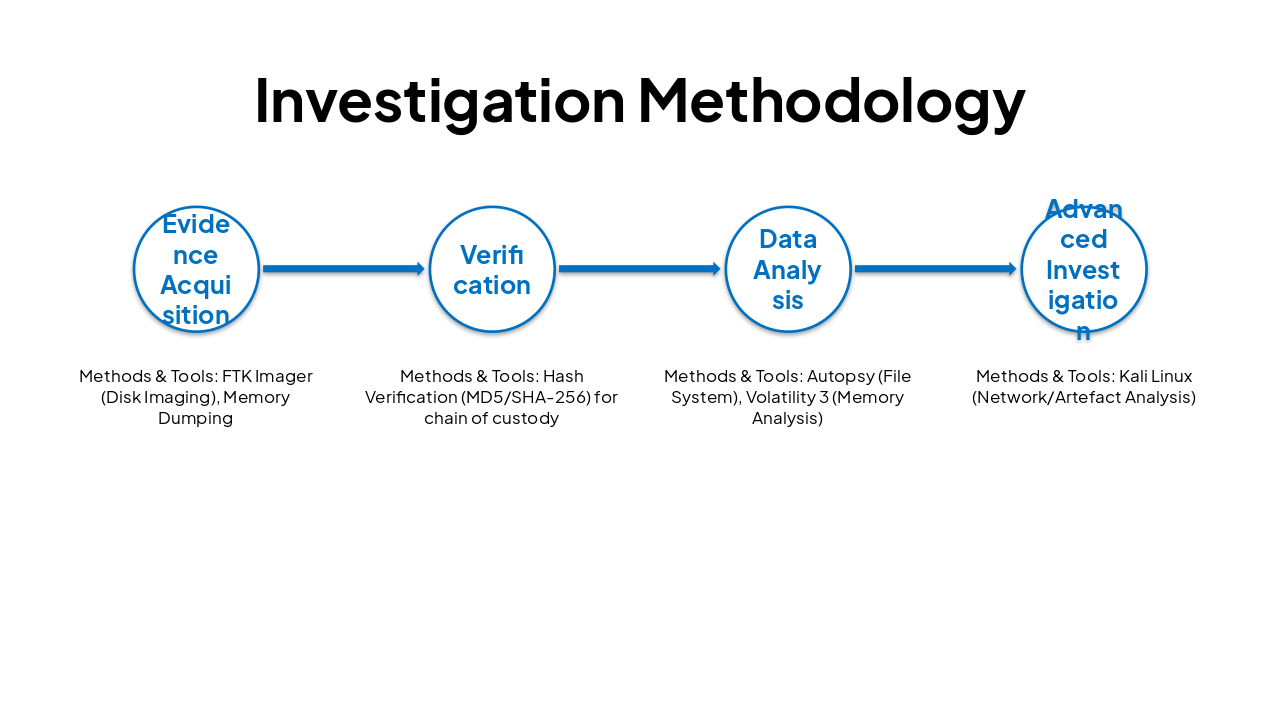
| Phase | Methods & Tools |
|---|---|
| Evidence Acquisition | FTK Imager (Disk Imaging), Memory Dumping |
| Verification | Hash Verification (MD5/SHA-256) for chain of custody |
| Data Analysis | Autopsy (File System), Volatility 3 (Memory Analysis) |
| Advanced Investigation | Kali Linux (Network/Artefact Analysis) |
---
Strong evidential findings demonstrate high probability of criminal coordination and intent.
Recommendations: Proceed with targeted email warrants, C2 IP infrastructure analysis, and cross-device digital forensics.
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.