Slide 1 - Information Security Training
Securing Our Future: Information Security Awareness
Employee Information Security Awareness Training | ISO/IEC 27001:2022 Compliance
---
Photo by Logan Voss on Unsplash
Generated from prompt:
Generate a fully downloadable ISO/IEC 27001:2022 Information Security Awareness Training PowerPoint for employees. 35–40 slides, professional corporate layout, icons, and visuals, with trainer notes for a 60-minute session. Include topics: introduction, ISO 27001 overview, ISMS, CIA triad, employee responsibilities, phishing/social engineering examples, password/MFA practices, incident reporting, Annex A controls, security do’s and don’ts, quiz, and key takeaways. Provide it as a fully downloadable PPTX link that works in any browser.
Employee training deck on information security aligned with ISO/IEC 27001:2022. Covers ISO 27001 overview, CIA triad, phishing & social engineering, password & MFA best practices, incident reporting, daily security habits, and a knowledge quiz to强化aw
Securing Our Future: Information Security Awareness
Employee Information Security Awareness Training | ISO/IEC 27001:2022 Compliance
---
Photo by Logan Voss on Unsplash
---
Photo by Misty Rose on Unsplash
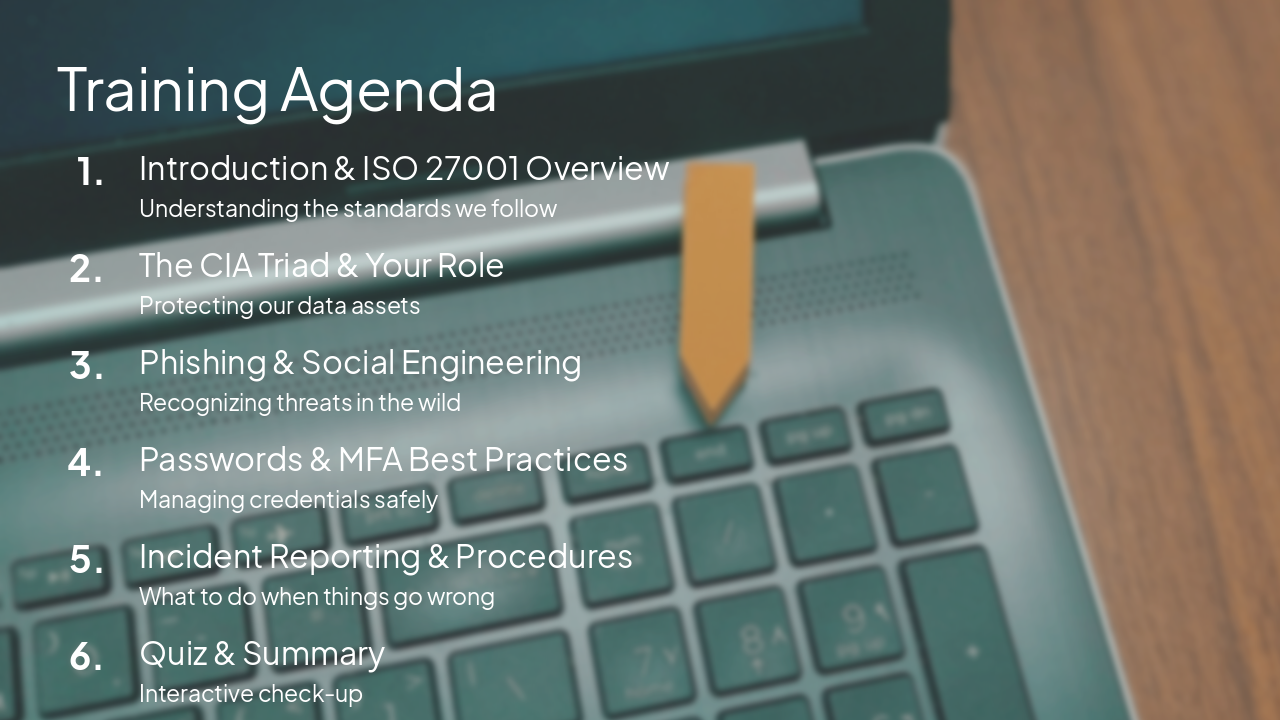
1
Why Information Security Matters to You
---
Photo by Maximalfocus on Unsplash

2
Understanding the Three Pillars of Security
🔒 Confidentiality Ensuring data is accessible only by authorized persons.
🛡️ Integrity Maintaining accuracy and completeness of data; preventing unauthorized modification.
✅ Availability Ensuring information and systems are available when needed by authorized users.
3
Staying Alert: Phishing and Social Engineering
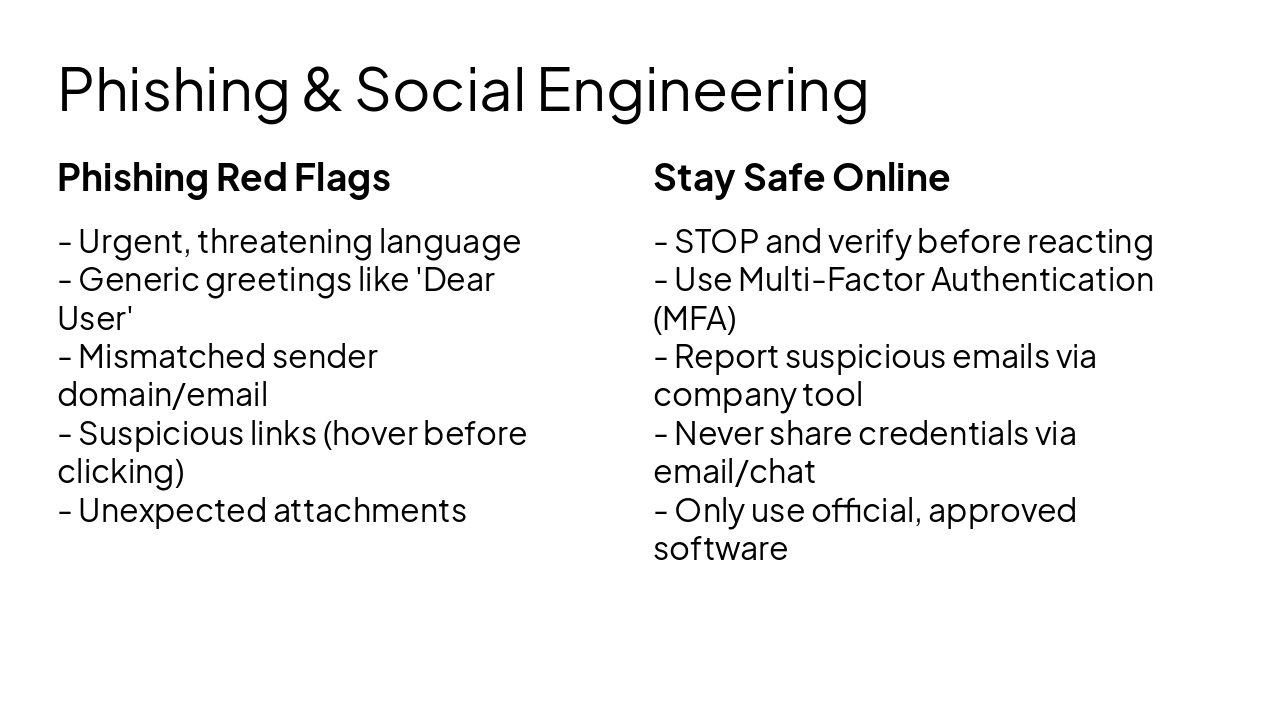
Phishing Red Flags
Stay Safe Online
4
Protecting Your Identity and Our Data
---
Photo by Parsoa Khorsand on Unsplash

5
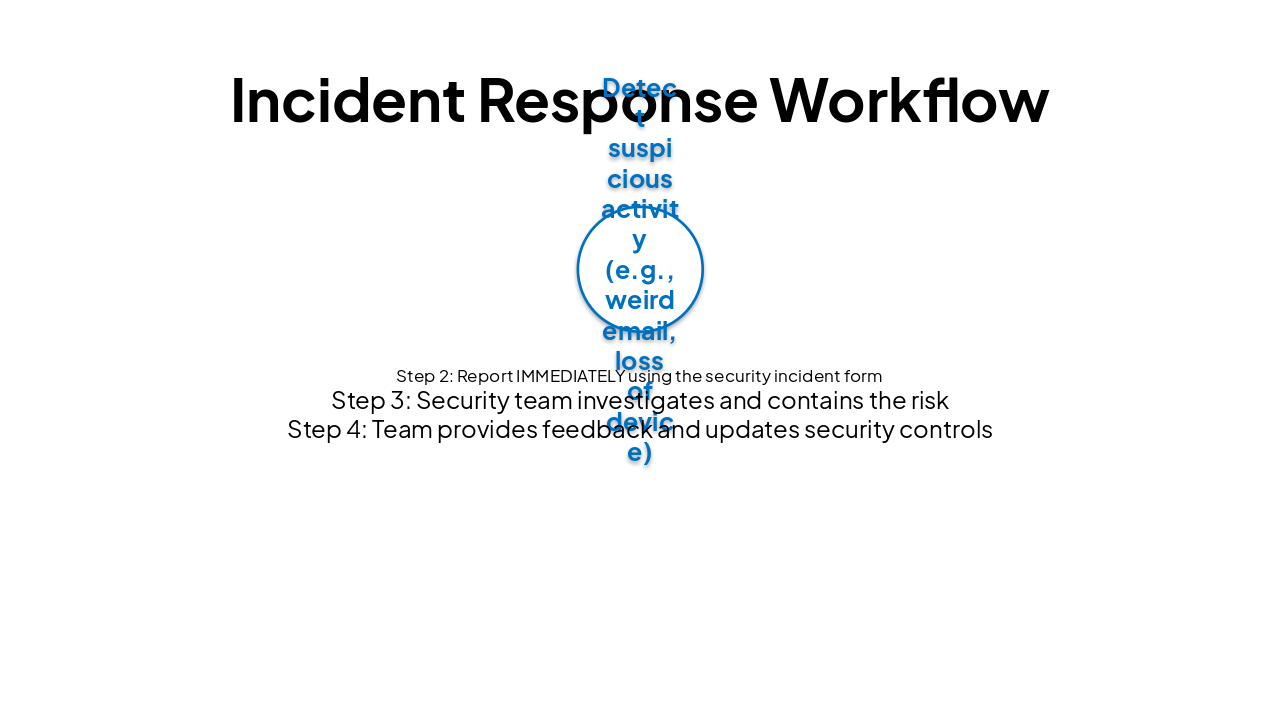
Your Role in Handling Incidents
---
Photo by Maik Winnecke on Unsplash

| Step 1 | Step 2 | Step 3 | Step 4 |
|---|---|---|---|
| Detect suspicious activity (e.g., weird email, loss of device) | Report IMMEDIATELY using the security incident form | Security team investigates and contains the risk | Team provides feedback and updates security controls |
6
Best Practices for Your Workday

Security Do's ✅
Security Don'ts ❌
7
Test Your Understanding
---
Photo by Adrian Newell on Unsplash

Stay Vigilant – Security is a Shared Responsibility
Thank you for helping keep our company secure! Contact the Security Team if you have any questions.
---
Photo by Johannes Plenio on Unsplash

Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.