Slide 1 - Title Slide
Securing Our Future Together: Information Security Awareness
Information Security Awareness Training (ISO/IEC 27001:2022)
---
Photo by Nastuh Abootalebi on Unsplash

Generated from prompt:
Create a 1-hour ISO/IEC 27001:2022 Information Security Awareness training presentation for all employees. Around 35–40 slides. Each slide must include detailed trainer/speaker notes so a facilitator can deliver a full 60‑minute session. Slides should have concise bullets while the speaker notes contain explanations, examples, and suggested talking points. Sections: title & objectives, importance of information security, real breach examples, overview of ISO/IEC 27001:2022, certification journey, CIA triad, what an ISMS is, employee roles and responsibilities, information classification and handling, acceptable use of company systems, passwords and MFA best practices, phishing and social engineering (with explanation examples), email and internet safety, cloud/file sharing risks, remote work and mobile device security, clean desk & clear screen, physical security basics, protecting personal and sensitive data, recognizing and reporting incidents, overview of Annex A controls relevant to staff, consequences of non‑compliance, what to do if a mistake happens, recap of employee do’s and don’ts, 5–7 question knowledge check quiz, closing and key takeaways. Include time guidance in the speaker notes so the trainer can stay within 60 minutes.
This 60-minute training deck on ISO/IEC 27001:2022 covers the importance of information security, CIA triad fundamentals, daily best practices like password security and data handling, threat recognition including phishing, incident reporting, and a知
Securing Our Future Together: Information Security Awareness
Information Security Awareness Training (ISO/IEC 27001:2022)
---
Photo by Nastuh Abootalebi on Unsplash

---
Photo by Nastuh Abootalebi on Unsplash
1
Why we care about ISO/IEC 27001:2022
---
Photo by Adi Goldstein on Unsplash
---
Photo by rc.xyz NFT gallery on Unsplash

2
CIA Triad and ISMS Fundamentals
---
Photo by Philipp Katzenberger on Unsplash
🔒 Confidentiality Only authorized people can access information.
✅ Integrity Ensuring information is accurate and hasn't been tampered with.
⚡ Availability Information is ready when it is needed.
---
Photo by Philipp Katzenberger on Unsplash
3
Your Role and Responsibility
---
Photo by Philipp Katzenberger on Unsplash
---
Photo by Vova Kondriianenko on Unsplash

4
Recognizing phishing, remote work, and incident reporting
---
Photo by Philipp Katzenberger on Unsplash

---
Photo by Philipp Katzenberger on Unsplash
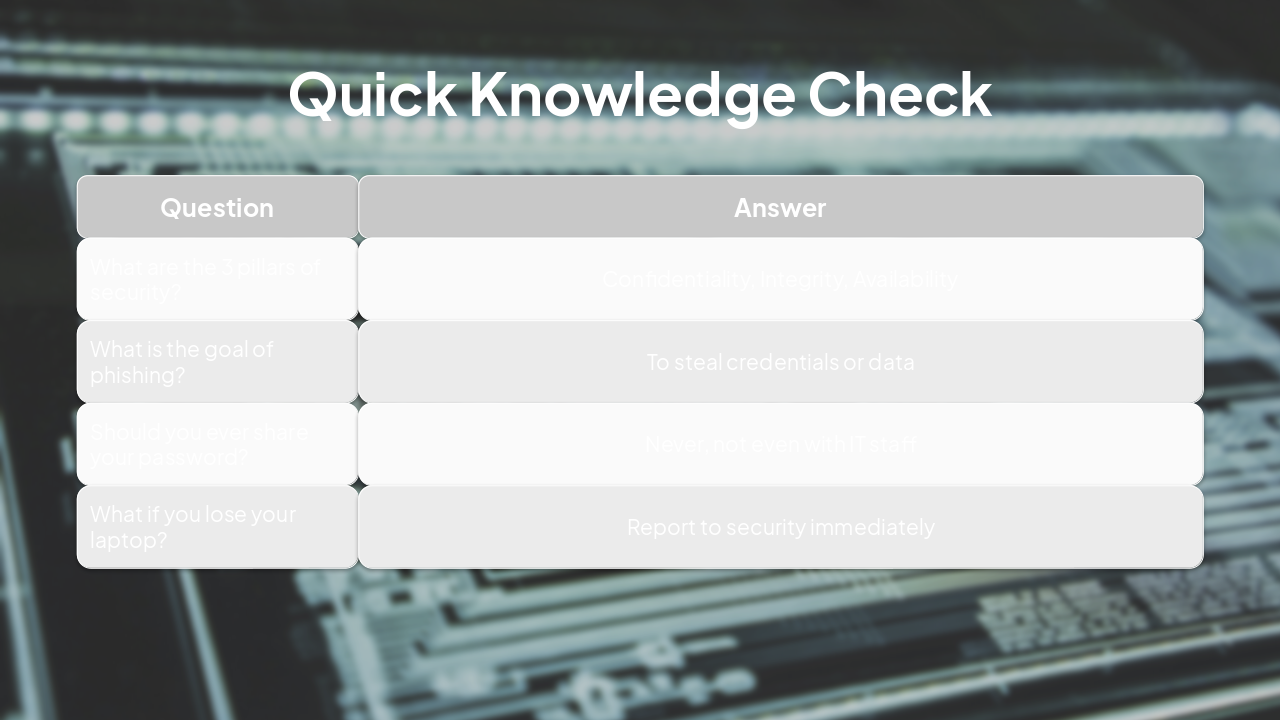
| Question | Answer |
|---|---|
| What are the 3 pillars of security? | Confidentiality, Integrity, Availability |
| What is the goal of phishing? | To steal credentials or data |
| Should you ever share your password? | Never, not even with IT staff |
| What if you lose your laptop? | Report to security immediately |
---
Photo by Adi Goldstein on Unsplash
Stay Safe: Your Security Matters!
Thank you for your attention. Together we protect our company. Questions? Email info-sec@company.com
---
Photo by Philipp Katzenberger on Unsplash

Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.