Slide 1 - Flutter Cyber Security Strategy
Flutter – Cyber Security Strategy & 6-Month Roadmap
Building a Scalable, Preventative, Engineering-Led Security Model
---
Photo by Albert Stoynov on Unsplash

Generated from prompt:
Create a professional executive-level presentation titled "Flutter – Cyber Security Strategy & 6-Month Roadmap". Tone: Strategic, leadership-facing, clear, outcome-driven. Design: Modern dark theme (deep navy background), subtle gradient accents in purple/blue, clean icons, minimal text per slide, strong visuals (roadmaps, dashboards, maturity curves, security architecture diagrams). Audience: Executive leadership & board-level stakeholders. Include speaker notes on every slide. Slide Outline: 1. Title Slide - Flutter Cyber Security Strategy - Building a Scalable, Preventative, Engineering-Led Security Model - Name / Date placeholder Visual: Abstract cyber network background with subtle glow. 2. Executive Summary - Current state: Federated brands, varying maturity - Goal: Scalable, engineering-first security platform - Outcome: Reduced systemic risk, faster brand onboarding, stronger governance Visual: 3 pillar graphic (Prevent, Govern, Scale) 3. Security Vision - Shift-left engineering - Central guardrails, local accountability - Identity-first risk reduction - Detection as code Visual: Security capability maturity curve (Reactive → Proactive → Predictive) 4. Current Challenges - Inconsistent security tooling - Variable brand maturity - Identity & privileged access complexity - Scaling SOC vs scaling engineering Visual: Multi-brand ecosystem diagram with fragmented controls 5. 6-Month Roadmap Overview Visual horizontal timeline: Month 1 | Months 2–4 | 6 Months+ High-level themes under each phase 6. Month 1 – Foundation & Assessment - Enterprise security posture review (internal & external) - Jurisdiction & regulatory mapping - Team capability & skills review - Stakeholder mapping - Initial gap assessment Visual: Assessment checklist graphic 7. Months 2–4 – Mobilise & Engineer - Take ownership of security tooling - Execute gap remediation plan - Strengthen team capability & hiring - Roll out updated security standards - POC new tooling & solutions Visual: Build/gear or platform engineering visual 8. 6 Months+ – Scale & Mature - Mature POC into live service - Central guardrail enforcement - Detection-as-code maturity - Follow-the-sun security model Visual: Globe graphic with continuous coverage 9. KPI Framework – Engineering-Led Security Introduce 5 KPI categories. Visual: 5-segment wheel or framework diagram 10. Preventive Engineering Controls (Shift-Left) KPIs: - % pipelines with enforced security gates - % IaC repos with mandatory scanning - Secrets detection rate (pre-merge) - % workloads deployed via approved templates - % cloud accounts under central policy enforcement Message: Reduce systemic risk before production. Visual: CI/CD pipeline diagram with security gates 11. Platform Guardrail Adoption KPIs: - % brands aligned to group baseline - % shared services under central guardrails - % workloads under central logging - Time to onboard new brand Message: Measure scalability, not SOC volume. Visual: Multi-brand architecture converging into central platform 12. Identity & Privileged Access Engineering KPIs: - % privileged access via PAM - MFA enforcement coverage - Time to revoke access (leavers) - Quarterly production access reviews Message: Identity risk > malware risk in regulated environments. Visual: Identity access flow diagram 13. Detection Engineering KPIs: - % critical threat scenarios covered - Time to deploy new detection - % detections defined as code - Telemetry coverage across shared platforms Message: Focus on capability build, not alert volume. Visual: Detection pipeline diagram 14. Operational Metrics (Supporting Indicators) - MTTR - False positive rate - Automation coverage Message: Lagging indicators of engineering maturity. Visual: Dashboard style metrics visual 15. Target Operating Model - Central security engineering - Brand-level integration - Shared services & standards - Follow-the-sun support model Visual: Operating model diagram 16. Expected Outcomes - Reduced systemic risk - Faster regulatory alignment - Improved scalability - Measurable security maturity growth Visual: Before vs After comparison 17. Closing Slide - Building a scalable, preventative, engineering-led security organisation - Q&A Visual: Clean minimal closing design Ensure slides are visually rich (icons, diagrams, light animations), executive-friendly, and concise. Include detailed speaker notes under each slide expanding on context and intent.
This deck presents Flutter's cyber security strategy, shifting to a scalable, preventative, engineering-led model. It covers executive summary, vision, challenges, 6-month roadmap (foundation, mobilization, scaling), KPI framework for preventive and検
Flutter – Cyber Security Strategy & 6-Month Roadmap
Building a Scalable, Preventative, Engineering-Led Security Model
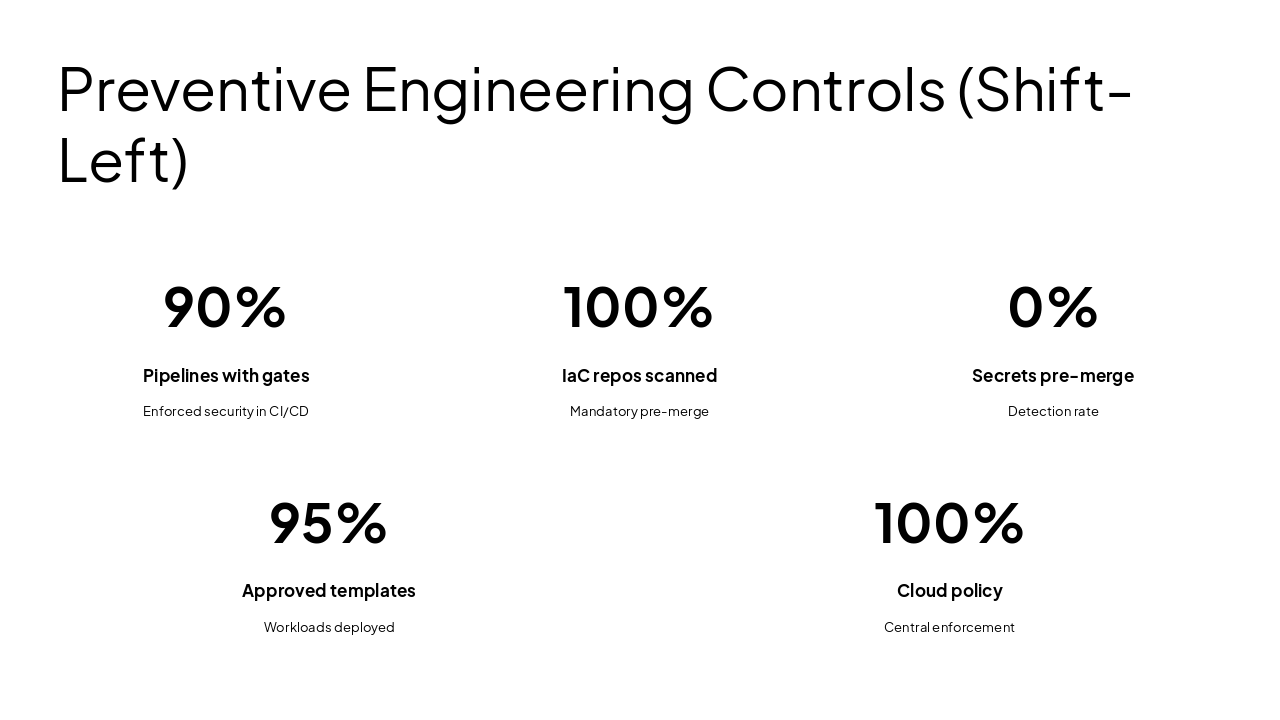
---
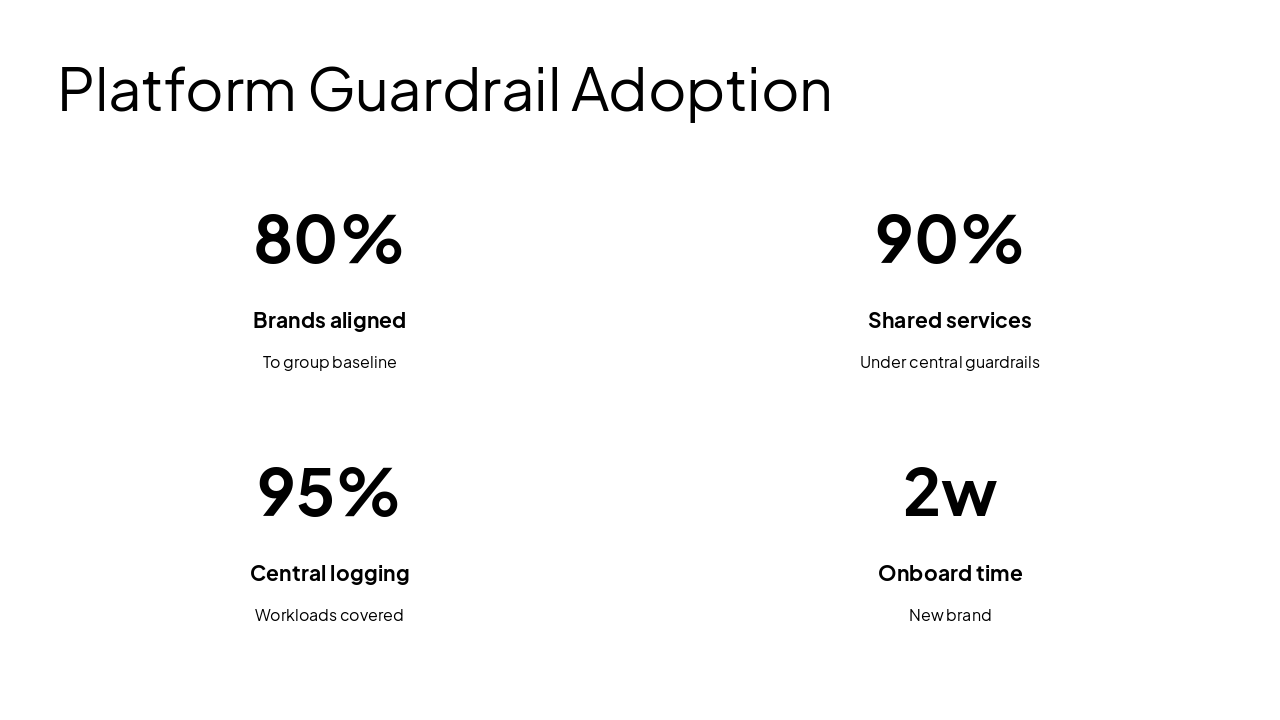
Photo by Albert Stoynov on Unsplash

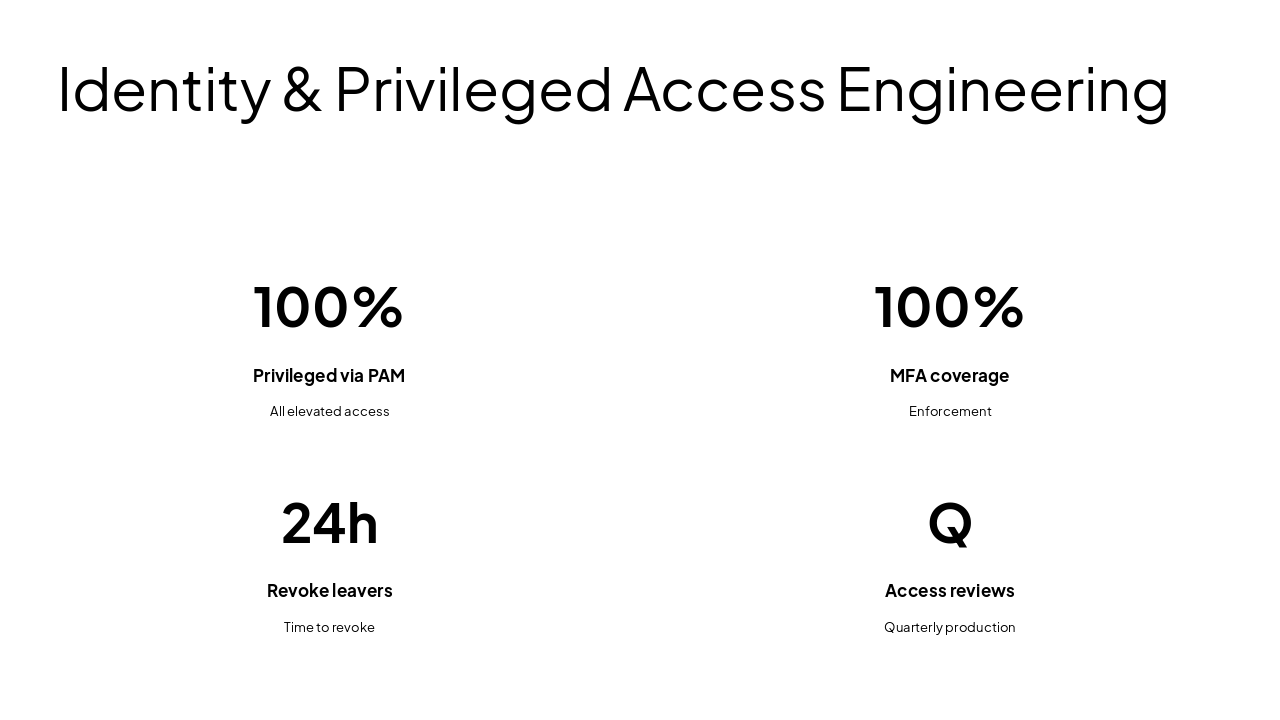
---
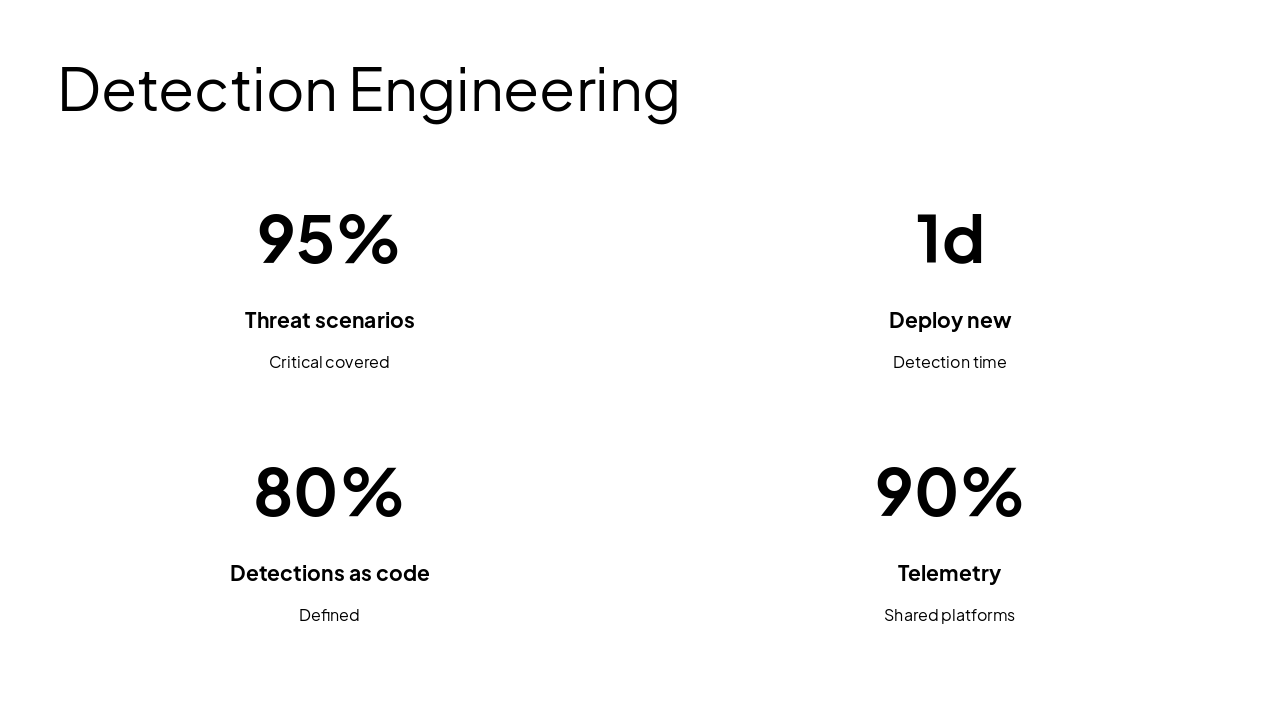
Photo by Sarah Sheedy on Unsplash
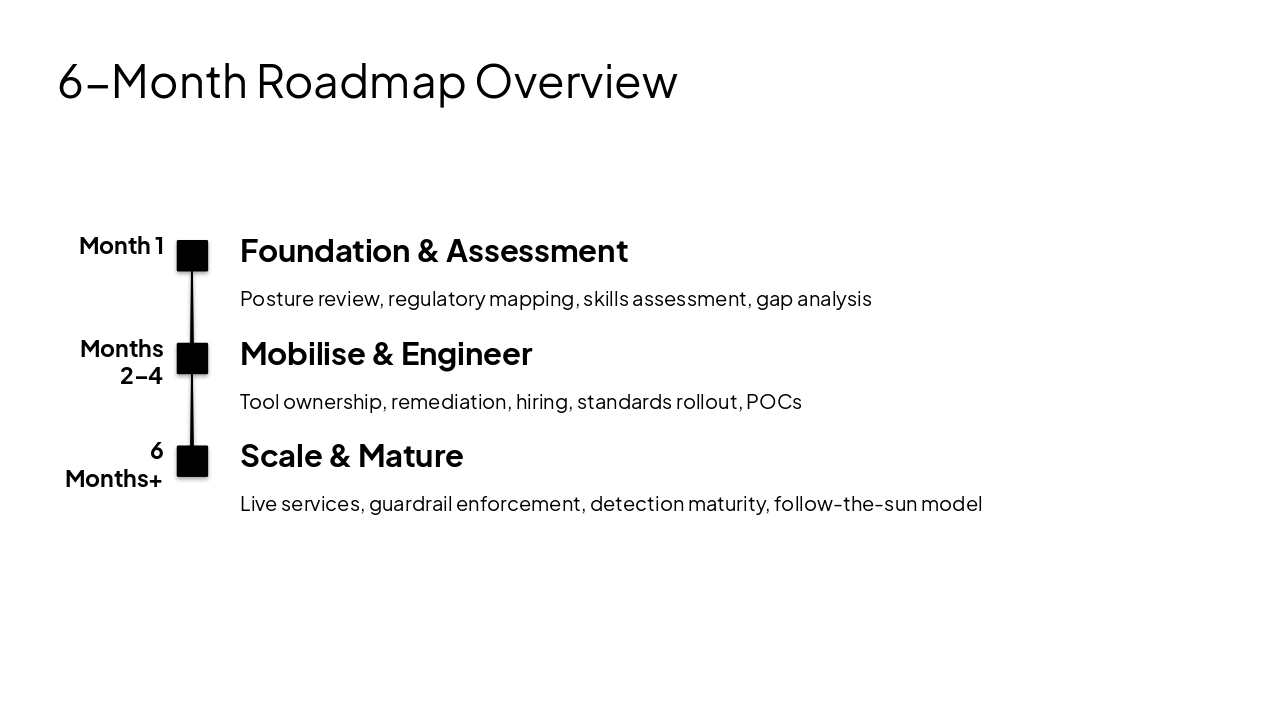
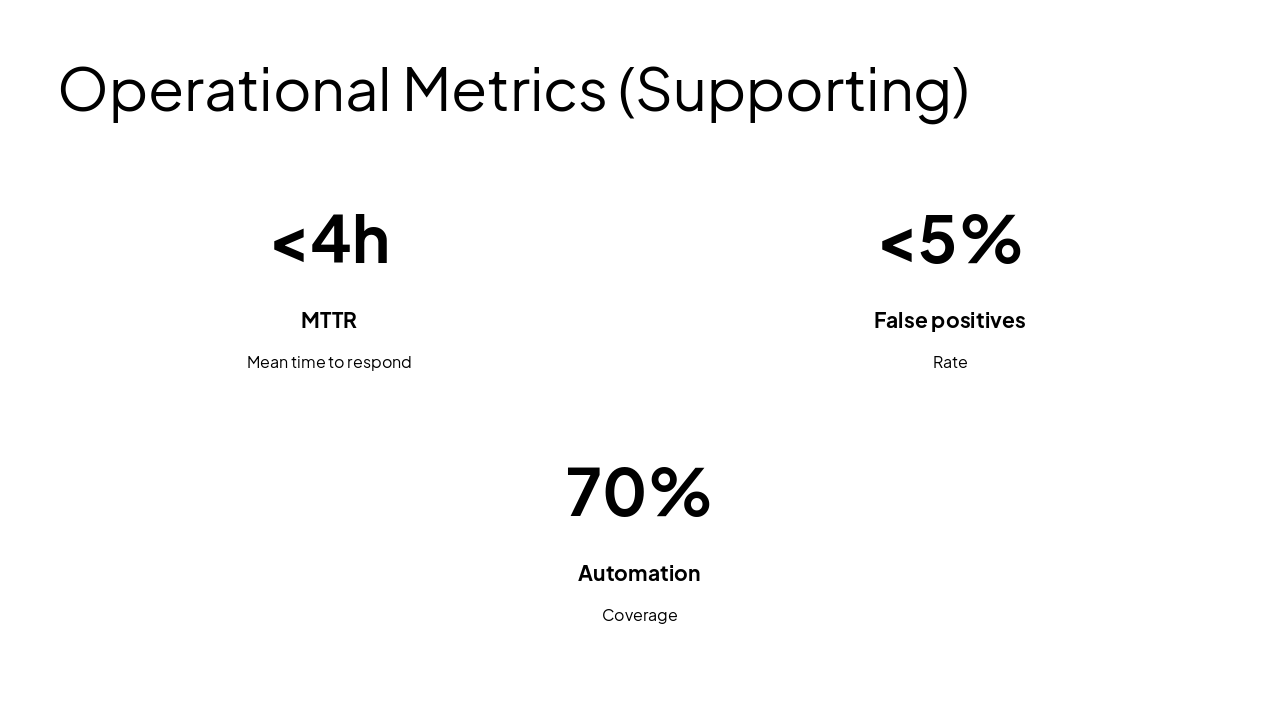
Month 1: Foundation & Assessment Posture review, regulatory mapping, skills assessment, gap analysis Months 2–4: Mobilise & Engineer Tool ownership, remediation, hiring, standards rollout, POCs 6 Months+: Scale & Mature Live services, guardrail enforcement, detection maturity, follow-the-sun model
---
Photo by Georg Eiermann on Unsplash
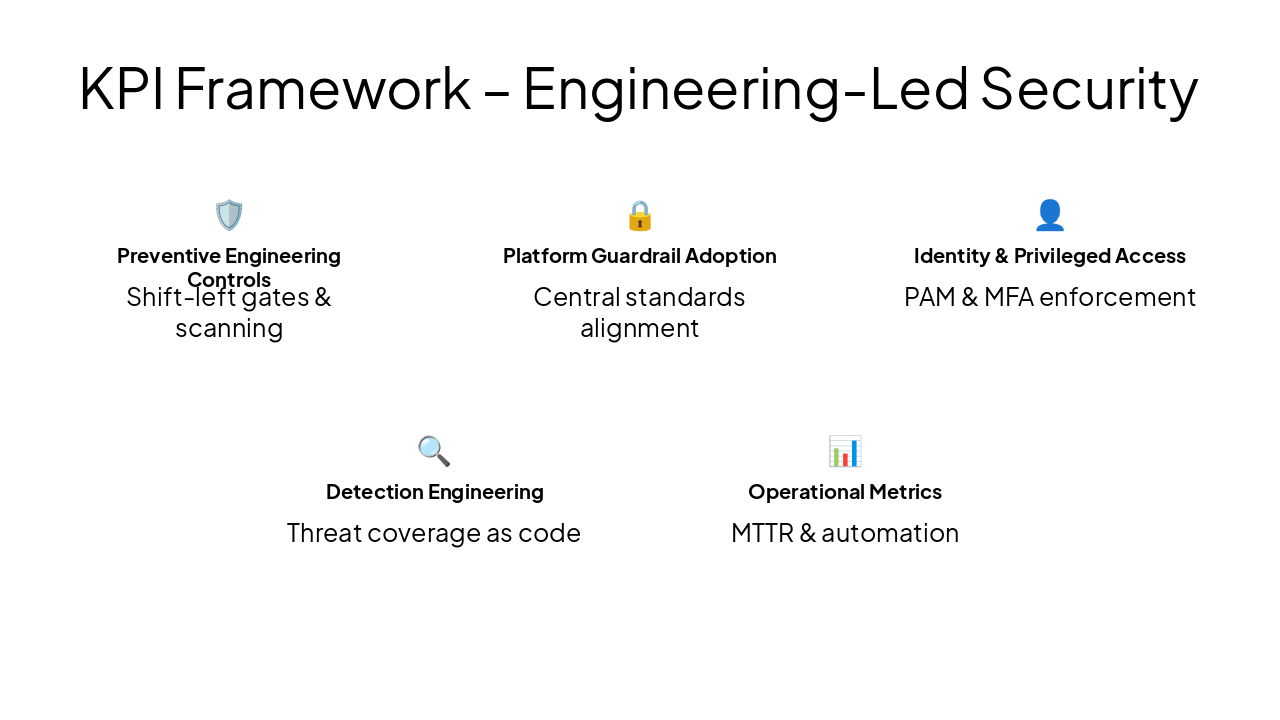
🛡️ Preventive Engineering Controls Shift-left gates & scanning
🔒 Platform Guardrail Adoption Central standards alignment
👤 Identity & Privileged Access PAM & MFA enforcement
🔍 Detection Engineering Threat coverage as code
📊 Operational Metrics MTTR & automation
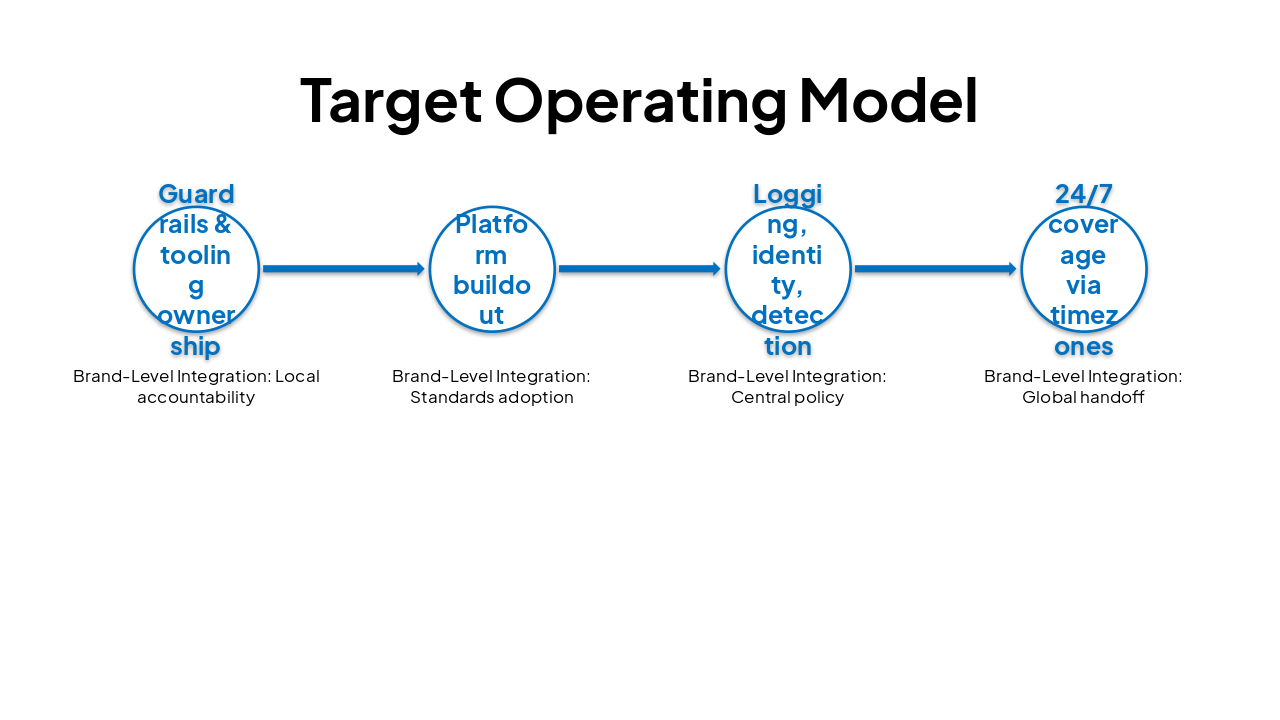
| Central Security Engineering | Brand-Level Integration | Shared Services & Standards | Follow-the-Sun Support |
|---|---|---|---|
| Guardrails & tooling ownership | Local accountability | ||
| Platform buildout | Standards adoption | ||
| Logging, identity, detection | Central policy | ||
| 24/7 coverage via timezones | Global handoff |
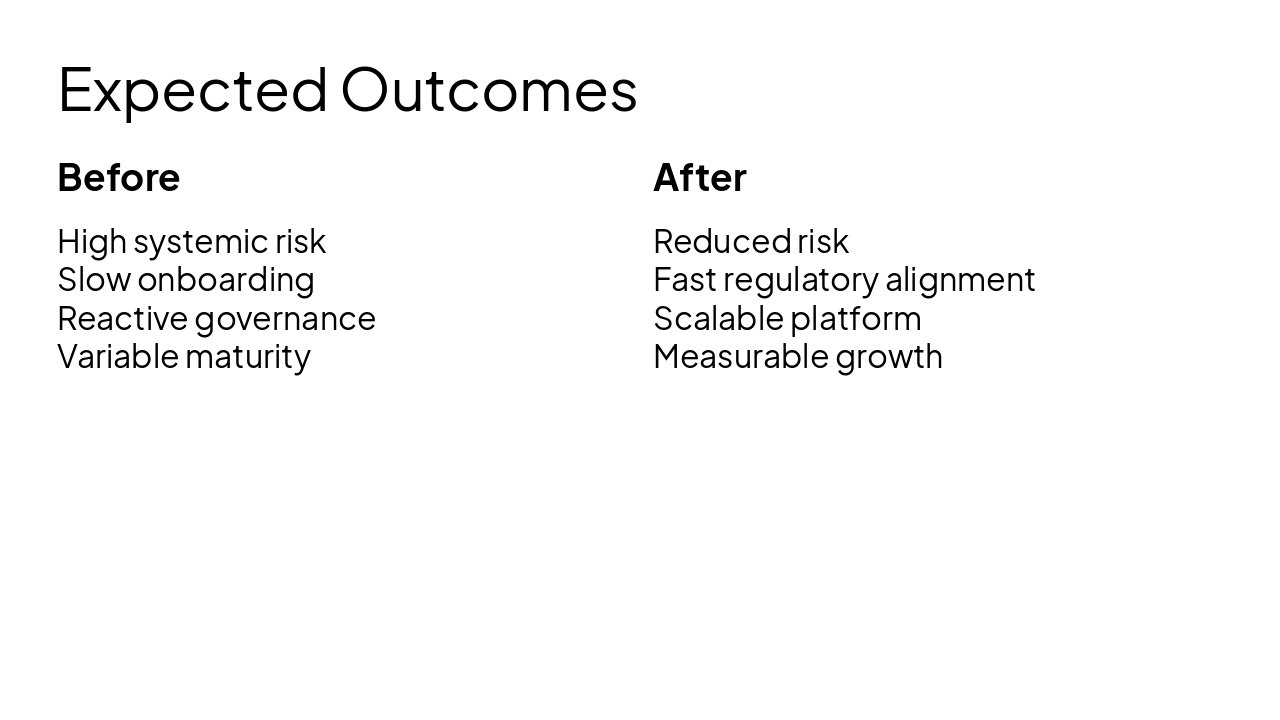
Before High systemic risk Slow onboarding Reactive governance Variable maturity
After Reduced risk Fast regulatory alignment Scalable platform Measurable growth
Building a scalable, preventative, engineering-led security organisation
Q&A
---
Photo by Amal S on Unsplash
Presentation Agenda
Strategy, Challenges, Roadmap, KPIs, Outcomes
---
Photo by Slidebean on Unsplash
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.