Slide 1 - Advanced Persistent Threats (APTs)
Advanced Persistent Threats (APTs)
Understanding Sophisticated Cyber Espionage and Targeted Attacks
---
Photo by Philipp Katzenberger on Unsplash

Generated from prompt:
make a presentation about Advanced Persistent Threats (APTs) in the cybercrime space
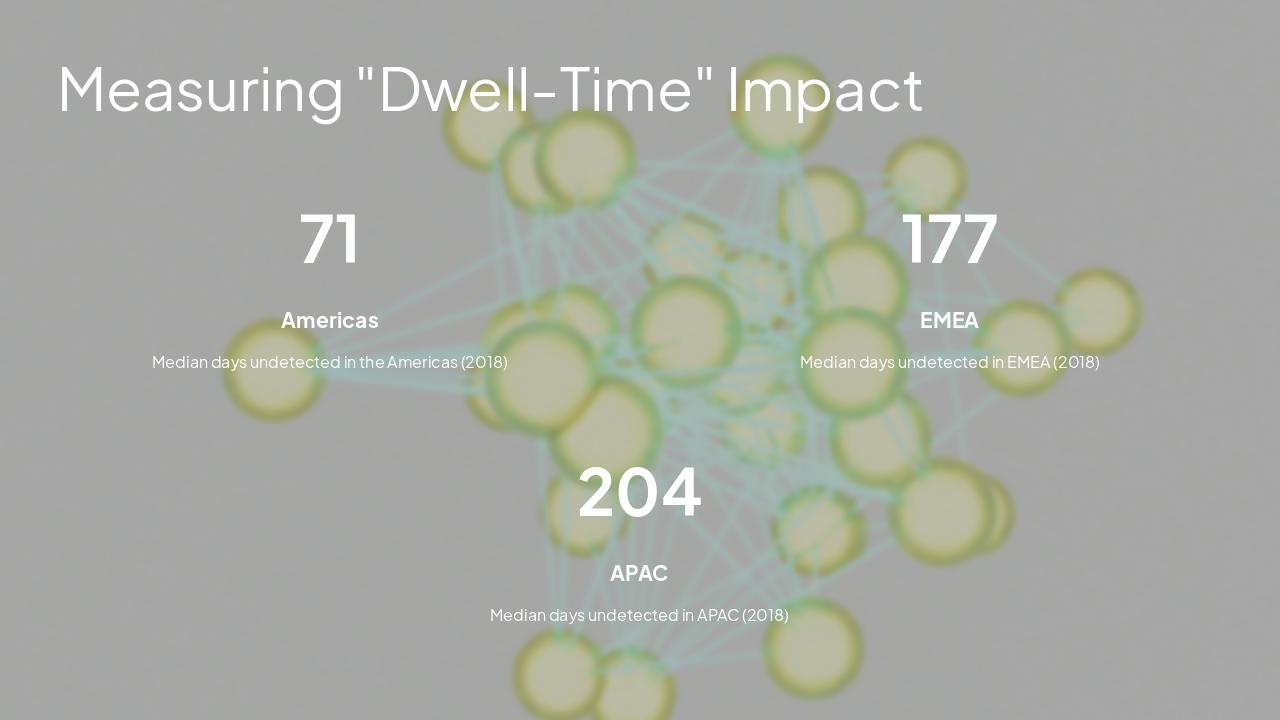
Explore Advanced Persistent Threats (APTs) through definitions, core characteristics, attack vectors, global dwell-time impacts, real-world case studies like Helix Kitten and Hainan APT Group, and essential strategies for detection, response, and pro
Advanced Persistent Threats (APTs)
Understanding Sophisticated Cyber Espionage and Targeted Attacks
---
Photo by Philipp Katzenberger on Unsplash

2
How these attackers operate and endure
---
Photo by Markus Spiske on Unsplash

---
Photo by Logan Voss on Unsplash
3
Examples of identified threat groups
---
Photo by NASA on Unsplash
Helix Kitten (APT34) Identified by CrowdStrike as an Iranian hacker group. Also known as OILRIG, Crambus, Cobalt Gypsy, Hazel Sandstorm, or EUROPIUM.
Hainan APT Group (40) Operated by the Hainan Provincial Department of State Security, responsible for secret policing in the province of Hainan, China.
Staying Ahead of Advanced Threats
APTs represent a sophisticated evolution in cybercrime, characterized by long-term stealth, persistence, and strategic state-backed motivations. Strengthening defense against these threats requires continuous monitoring, rapid incident response, and proactive threat intelligence.
---
Photo by Kedibone Isaac Makhumisane on Unsplash
Explore thousands of AI-generated presentations for inspiration
Generate professional presentations in seconds with Karaf's AI. Customize this presentation or start from scratch.